the bait
It started with a follow.
The follow itself is the work. On X, if a stranger DMs you without you following them back, the message lands in the filtered "message requests" inbox where it dies. Following first is how the operator earns the right to ping your notifications directly, so the play is simple: follow the target, wait for a follow-back, then open with something innocent.
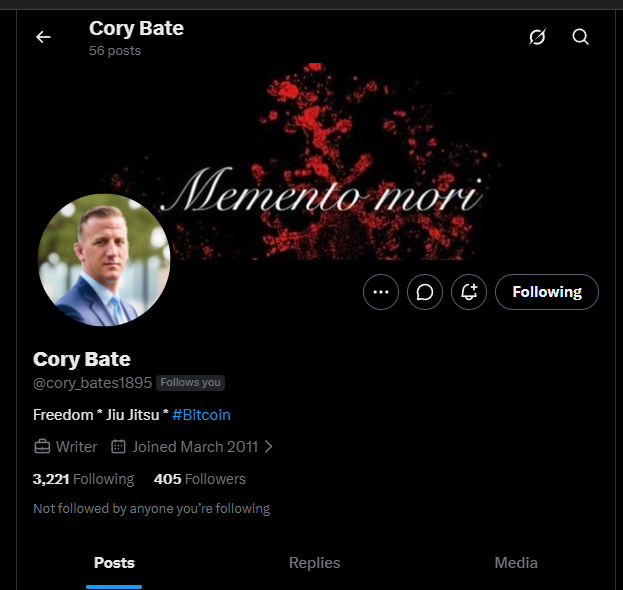
Cory's profile is calibrated for plausibility. Joined in 2011 (an aged account is a meaningful signal; freshly-created burner accounts get filtered everywhere). Bio reads "Freedom · Jiu Jitsu · #Bitcoin" so the cover story explains why a stranger would slide into your DMs about crypto. The display photo is a generic professional headshot, the banner is a stylized "Memento mori" graphic. The follower-to-following ratio (405 followers, 3,221 following) is exactly what you'd expect from a low-effort engagement-farming account that aggressively follows in hopes of follow-backs.
I followed back.
the slow burn
He opened with a single word.
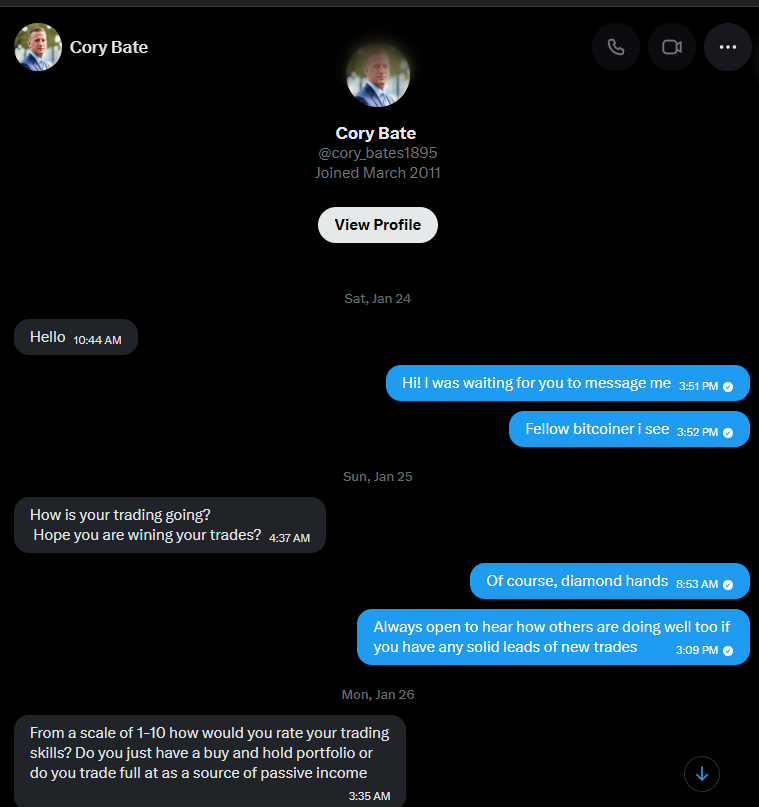
Notice the pacing. Saturday: "Hello." Sunday: a check-in. Monday: a qualification question. He is not in a rush. Pig-butchering operators run dozens of these conversations in parallel and the slow tempo is a feature, not a bug. It conditions the target to expect a casual, friendly relationship instead of a sales pitch.
The qualification question is the key beat: "rate your trading skills 1 to 10" and "buy-and-hold or active source of passive income." He is not asking because he cares. He is asking to bucket me into a script branch. Self-described novice gets one funnel, self-described pro gets another. I picked "diamond hands" so he knew exactly which playbook to open.
He opened the right one on Tuesday.
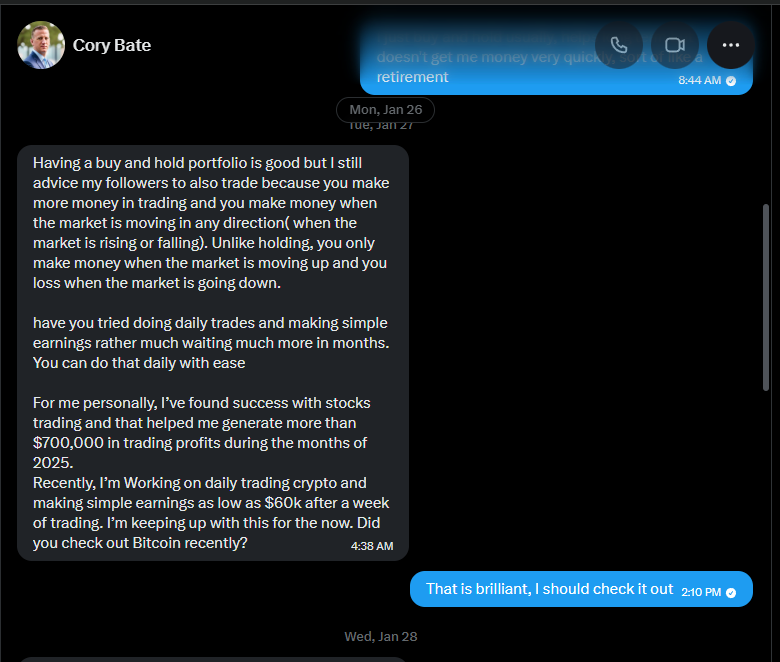
The pitch hits every classic: vague authority ("I advice my followers"), specific numbers ("$700,000", "$60k"), the made-up edge ("you make money in any direction"), and the soft close ("did you check out Bitcoin recently"). The grammar is consistently a half-step off in ways that read as ESL ("I advice", "you loss", "wining your trades"), but it's coherent enough to feel like a busy person tapping on a phone if you're not looking for it.
I was looking for it. Every one of those tells (the impossible specificity of "$700K in 2025" with no mechanism, the ESL syntax, the boilerplate cadence, the unsolicited DM about money from a stranger I had never spoken to) registered as exactly what they were the moment they hit the screen. The point of the engagement is not to find out whether he is running a script. The point is to find out which script and where it leads. The only way to map the funnel end to end is to walk into it on purpose and play the part.
For somebody without that prior, none of this is obvious in real time. There is a face on the profile, an aged account, a friendly tone, and a slow casual relationship instead of a sales pitch. The tells I'm cataloging here are tells because I am cataloging them in writing. In the moment, embedded in a normal-feeling conversation, the threshold for "this feels off" is a lot higher than people imagine. That is the whole game. The reason this funnel works on intelligent people who absolutely know that crypto scams exist is that it never feels like a pitch until it is already too late.
So I let him keep cooking.
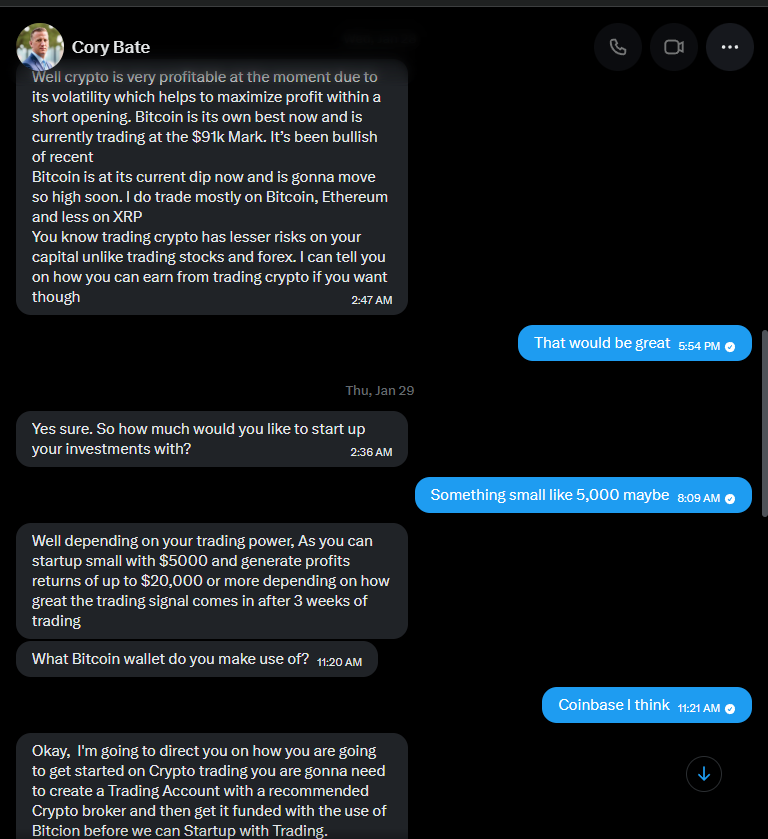
This is the qualification stage. He needs four things before he can drop the link without it looking forced:
- An expressed amount. I gave him "$5,000" and he immediately quoted me "$5000 to $20,000 in 3 weeks", a 4x in 21 days. Quoting absurd returns to the target is itself a filter. People who think those numbers are reasonable are the people who will deposit. People who flinch at the math self-eject from the funnel and save him time.
- An exchange. I said "Coinbase". He now knows the path my money would take to reach his wallet (USD bank deposit to Coinbase, USD to BTC inside Coinbase, BTC withdrawal to whatever address the platform shows me).
- A wallet posture. "What Bitcoin wallet do you make use of" is not curiosity. It is checking whether I have any self-custody experience. Self-custody users tend to ask uncomfortable questions about who controls the keys on the "trading platform". I gave him a centralized exchange answer and stayed in his comfort zone.
- An investment narrative. "Passive income, diamond hands, willing to start with $5K" tells him exactly which script to load.
Then came the drop.
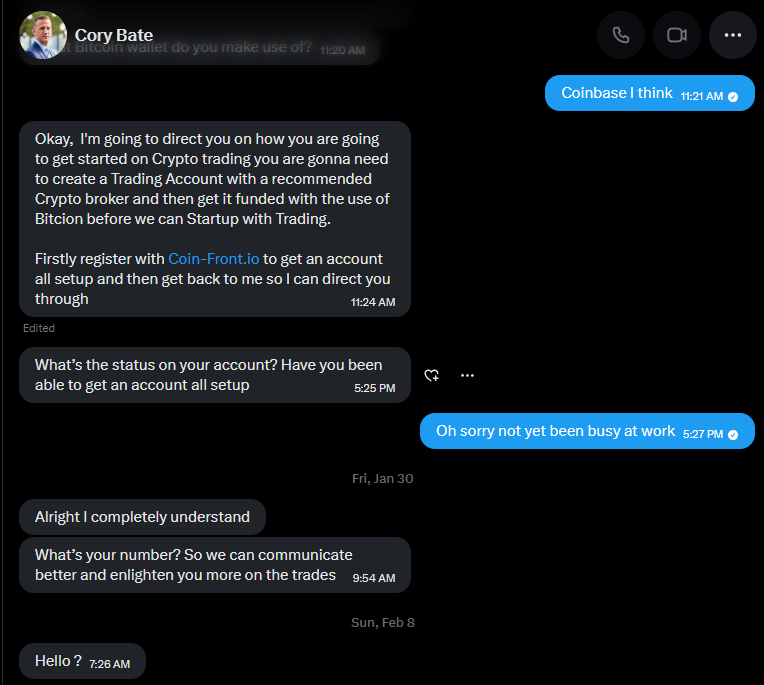
Coin-Front.io. Note the message is marked "edited" in the screenshot, which means he typo'd it the first time and went back. Operators running the same script across many targets sometimes muscle-memory the wrong domain into the chat. Edits on the drop message are a tell that this is a templated funnel.
The followups are textbook. "What's the status on your account" is the chase. "What's your number, so we can communicate better" is the off-platform pivot, getting the target onto SMS or WhatsApp where there is no visible record for X to act on later. "Hello?" two weeks later is the re-engagement attempt for cold leads.
I went and looked at the platform.
the platform
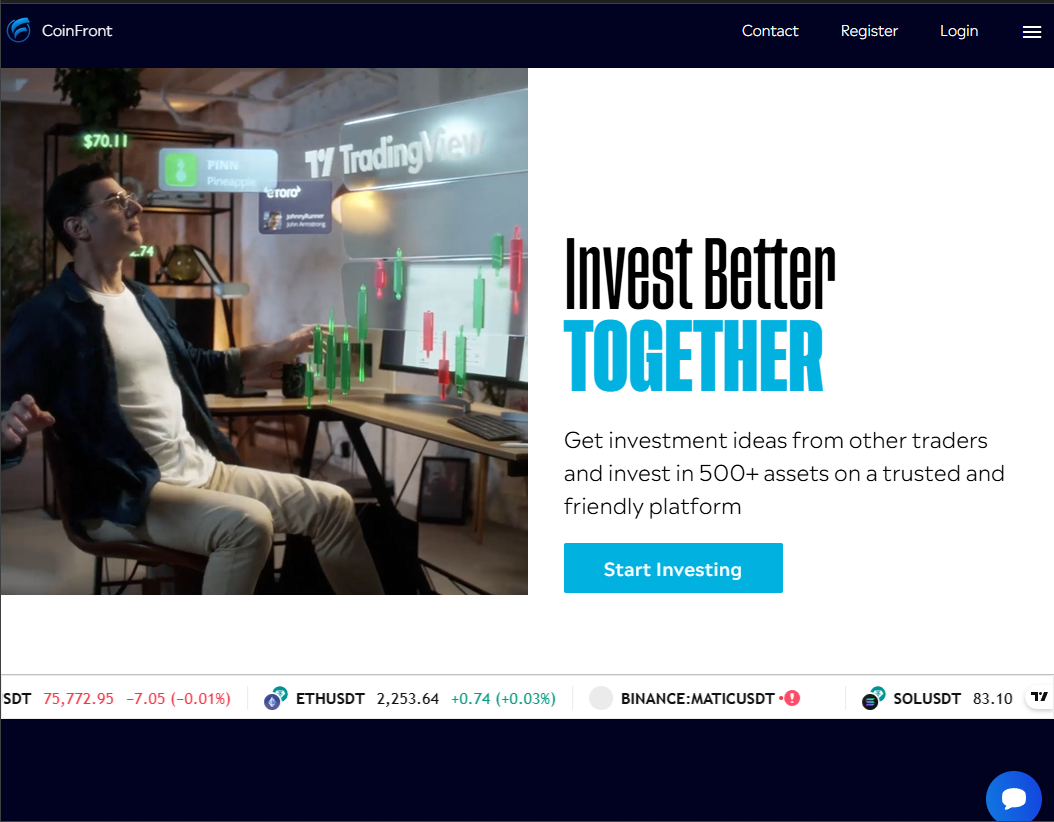
The landing page is competent. Not great, competent. The hero copy ("Invest Better TOGETHER") is meaningless. The stock photo of a man surrounded by TradingView holograms is an AI-generated or heavily-licensed image that has been bouncing around dozens of these operations since at least 2024. The bottom ticker is the real TradingView widget pulling live BTC/ETH/MATIC/SOL prices, which is a free embed anyone can drop on any page in five minutes. Real prices on the marquee make the dashboard feel alive.
Pulling the page source gave me the meta description: "CoinFront, Forex, Stocks, ETFs and Options, Online Trading Platform". Cory pitched it as crypto. The site advertises Forex/Stocks/ETFs/Options. That mismatch is one of the cleaner tells: the storefront is a generic asset-management theme, but the playbook the operator is reading is the crypto one. They have multiple scripts pointed at the same kit.
Then it asked for permissions.
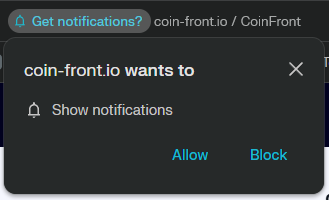
This is one of the more underrated weapons in this whole genre. If you click Allow, the site can push system-style notifications to your browser for as long as you have it installed. Those notifications can fire when you are on completely unrelated pages, can mimic banking or shipping alerts, and can carry links to other scams entirely. It is also a cheap way to re-engage somebody who closed the tab and never came back, which is precisely what most targets do after the first visit. Block.
The signup form wants everything.
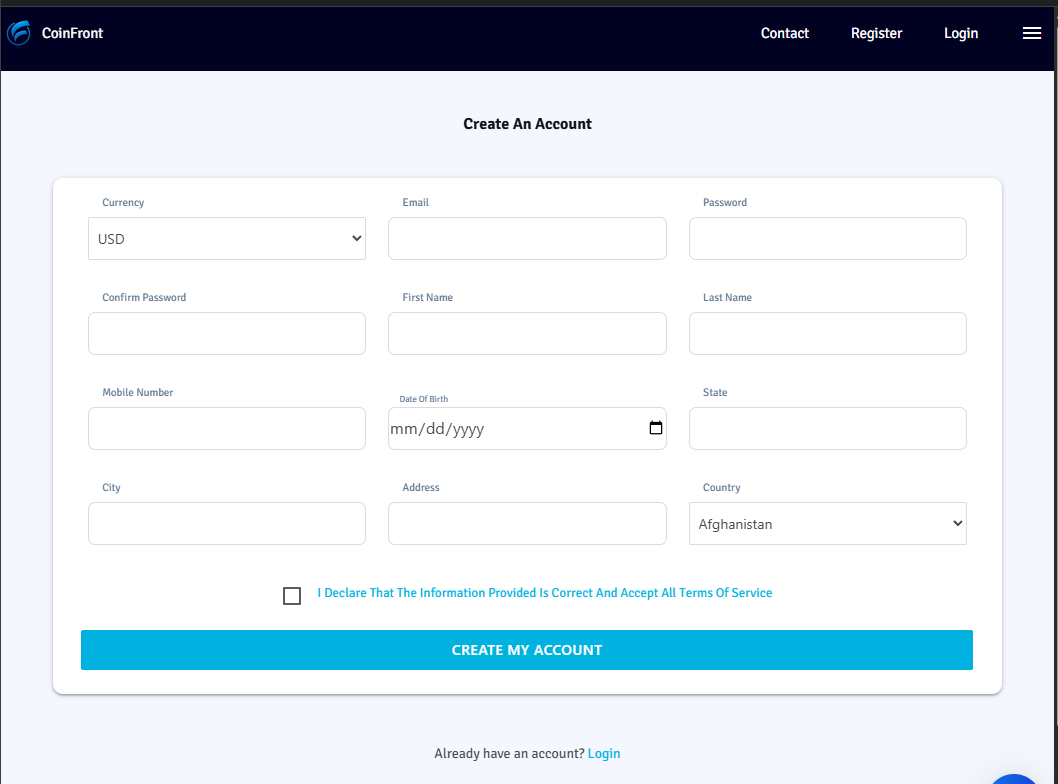
Email, password, full name, mobile, DOB, full address, country. A real broker collecting that much PII would have a privacy policy, a regulator listed in the footer (FCA, FINRA, CFTC, ASIC, something), and a working "Contact" link that goes somewhere other than a styled lead-capture form. CoinFront has none of that. The Country dropdown defaults to Afghanistan, which is a small thing but a meaningful one: the form was clearly built without ever localizing for any specific market, so the operators just took whatever the alphabetical first entry was.
I always register on platforms like this with the username Admin / User. Not because the operators care what name I gave them, but because it gives me a tripwire. Any future "personalized" email, SMS, or call addressing me as "Admin" is provably from data harvested off this exact form (or sold downstream from this one). When Admin User shows up in a breach dump six months from now, I have a clean line back to which scam shop did the harvesting.
After registration, KYC.
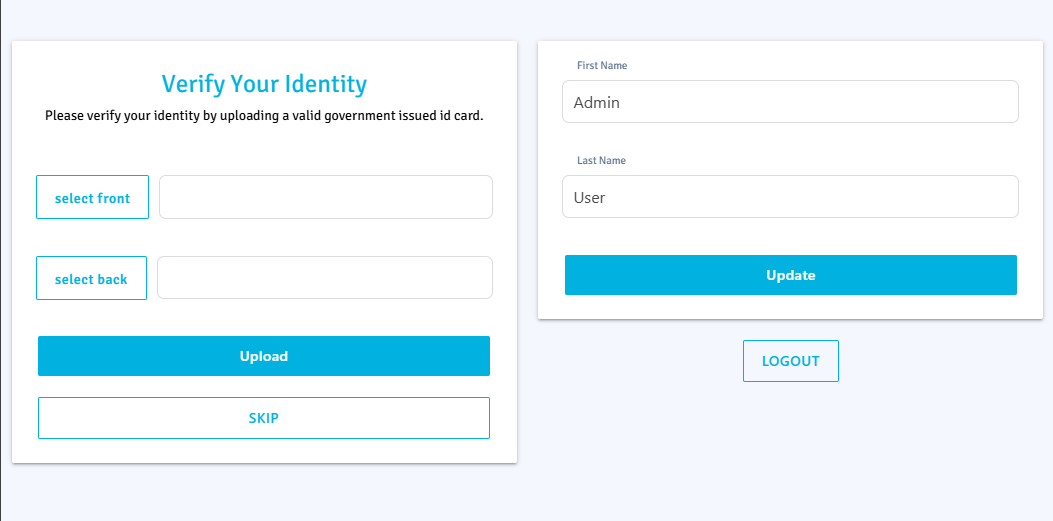
KYC theater is one of the most dangerous moves in this entire funnel. A real licensed broker has to do KYC by law and has zero ability to skip it. CoinFront has a Skip button. The Skip button is there for skeptical targets who refuse to upload ID, so the funnel can keep running and harvest the deposit anyway. The Upload button is there for everyone else, and that "everyone else" hands over their driver's license or passport to a Lithuanian-hosted PHP kit run by people who have already lied to them about every other thing.
What happens to the IDs? At minimum they get sold in identity-fraud markets. At maximum, they get used directly to open accounts at real exchanges or to bypass KYC at services where the operator wants to launder. The dashboard's pending-verification dialog references a /uploads/ directory on the server. Listing that directory was 403'd at the front proxy when I checked, but the directory itself exists, which means the IDs land in a real filesystem path under the webroot. If the operators ever lose control of the box, every single ID submitted to this site walks out at once.
I skipped.
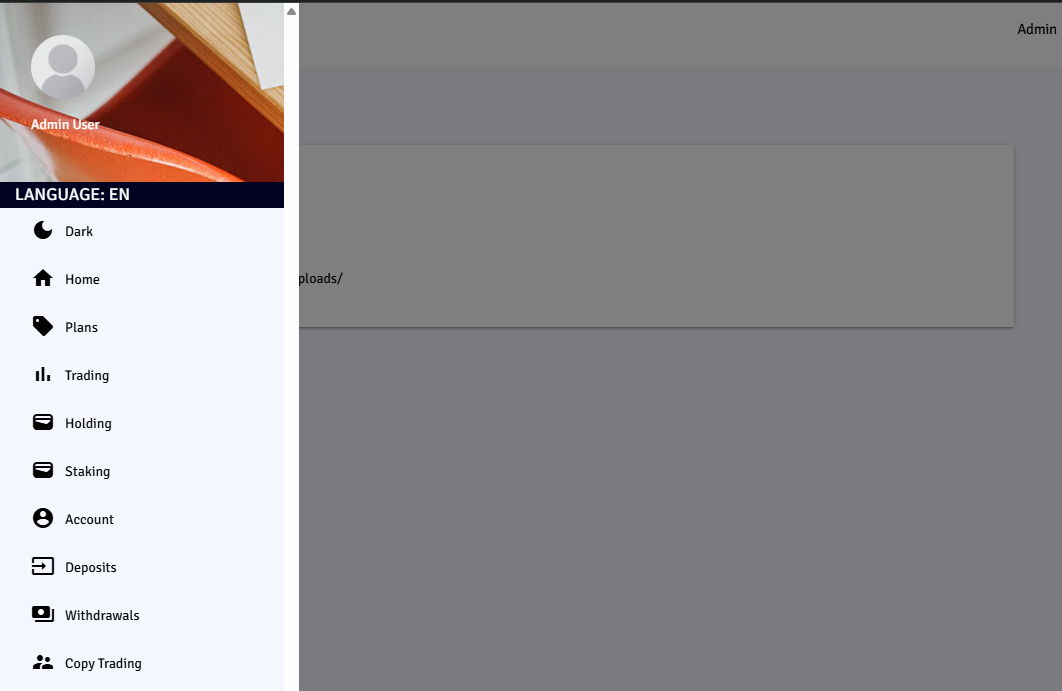
The sidebar is the giveaway. The lineup, Plans / Trading / Holding / Staking / Account / Deposits / Withdrawals / Copy Trading, in exactly that order, with that icon set, is the canned panel-set you see across hundreds of these "investment platforms". This is an off-the-shelf PHP kit. The same theme, the same nav order, the same icons get rebadged with a new logo and a new domain every few weeks. The operator's job is not to build the platform. The operator's job is to drive traffic to it and convert.
Then they held my account "pending verification". Which is the cue for me to come back to Cory and report in, so he can warmly walk me through funding the account, and then we are off to the races. I did not come back. I went looking under the hood instead.
under the hood
What follows is what you can learn about a site like this in about an hour with no special access. None of this is exploitation, just observation.
the domain
WHOIS on coin-front.io:
- Registered 2025-05-15 at PDR Ltd. (PublicDomainRegistry.com), an Indian registrar that is the de facto default for low-cost throwaway scam domains. Registrant data is GDPR-masked.
- The record was last updated 2026-04-29 21:49:49Z, status
renewPeriod. That timestamp is roughly two hours before I started writing this. They renewed the domain today. They are still investing in keeping it live, which means it is still converting somebody.
the archive
Wayback Machine has three captures of coin-front.io:
- 2025-07-16: 1,340 bytes, just a placeholder page.
- 2025-08-06: 1,360 bytes, identical digest to July, still placeholder.
- 2026-04-30 00:06:47Z: the live site, captured by me as part of writing this case file.
The aged-domain-then-weaponize pattern matters. The site was parked for at least three weeks visible to Wayback in mid-2025, then went live with the trading-platform content sometime between August 2025 and now. Some email gateways and corporate SOCs apply additional scrutiny to "young" domains under 90 days old. By the time CoinFront started DMing targets, the domain itself was ten months aged. The kit on top is new, the registration is not.
the cert
TLS is a Let's Encrypt R12 wildcard (*.coin-front.io), valid Mar 16 2026 to Jun 14 2026. Standard 90-day rotation. Nothing notable except the wildcard itself, which suggests the operators planned to spin up subdomains (likely region-specific like us.coin-front.io or affiliate-specific like cory.coin-front.io) at some point. None resolve right now.
the host
coin-front.io resolves to 85.206.242.4 and 2a04:2180:dc05:c108::4. The IP belongs to BACloud (Informacines sistemos ir technologijos, UAB), AS61272, a budget VPS provider in Šiauliai, Lithuania. The reverse DNS hostname is cl08.bacloud.online, which tells us this is shared web hosting on BACloud's cluster #8. A reverse-IP lookup against that address returns roughly 40 unrelated domains, a mix of legitimate small business sites and a couple of obvious siblings (forex signal services, generic credit-product brand names). I am not publishing the neighbor list because the legitimate sites on the same shared host had nothing to do with this scam, and burning their reputations would be unfair.
The site itself runs PHP behind LiteSpeed, with an OpenResty front proxy doing aggressive bot-shielding (any request that looks like a real browser gets a "One moment, please" interstitial that reloads after five seconds, while requests with non-browser user agents get blanket HTTP 415 responses). It also loads web3.js and @walletconnect/web3-provider, so in addition to the "deposit BTC to this address" flow they support a direct wallet-connect drain path for victims who have a browser wallet installed. There is a Smartsupp live-chat widget bottom-right, which means there is a human on the other end of the chat ready to push hesitant targets the rest of the way through the funnel.
After roughly an hour of polite probing of the site and its neighbors, my egress IP got firewalled off the entire BACloud edge. The site was confirmed still up from external probes in Brazil, Turkey, the UK, and the US, with sub-second response times. The block on me is the WAF doing its job, which is itself a useful data point: this is not a $50 PHP install on a forgotten box, it is a kit-and-shield setup with someone watching the logs.
the score
| score | reasoning | |
|---|---|---|
| convincing | 4 / 10 | The X persona is well-aged and the slow tempo is patient. The grammar errors and the pitched returns ($5K to $20K in 3 weeks) make it a four for anyone with even a casual prior on what real markets do. For a true beginner, push this to a six. |
| sophistication | 3 / 10 | Off-the-shelf PHP kit, shared hosting, no original infrastructure. The interesting tradecraft is the social pacing on X, not the platform itself. |
| scalability | 8 / 10 | One operator can run dozens of cory_bates1895 accounts in parallel, all funneling to the same site. The kit supports unlimited concurrent victims. The bottleneck is X account aging, not platform capacity. |
| danger | 7 / 10 | The combined ID upload and PII collection is more dangerous than the cash loss. Anyone who completed KYC on this site had their driver's license or passport sitting in a /uploads/ directory on a Lithuanian shared host. Identity damage outlives the wire transfer. |
what would have happened next
If I had funded the account with the proposed $5,000, the script from cases like this is well-documented:
- The dashboard would show fake P&L in my favor. The chart goes up. Cory would warmly congratulate me and suggest doubling down to "lock in the next signal."
- After two or three weeks of paper gains, I would try to withdraw. The withdrawal would fail with a "verification fee" or "tax clearance" required, payable in BTC. That fee would be a fraction of the supposed balance, designed to feel small relative to the gains on screen. Pay it, and the next withdrawal attempt fails for a different reason. Pay that one, and the next.
- At some point I run out of money or out of patience. Cory goes quiet. The site starts loading slowly, then not at all. A few weeks later a "recovery specialist" reaches out claiming to have a way to get my money back, for a fee.
Total realistic loss for a fully-engaged target on this exact funnel is in the $15K to $50K range before they stop paying, plus whatever follow-on damage the ID upload causes.
the disclosure trail
This case is published with the operation still live. The disclosure work goes out in parallel with publication:
- X: report
@cory_bates1895for platform manipulation and financial fraud, with the DM transcript attached. - PDR Ltd. (registrar): abuse complaint to
abuse@publicdomainregistry.comwith the WHOIS, the screenshots, and the live-funnel context. PDR's track record on these is mixed at best, but the report goes in. - BACloud (host): abuse complaint to
noc@bacloud.comwith the IP, the hostname, and the same evidence package. BACloud has a higher hit rate than the registrar in my experience. - Wayback: three new snapshots saved (homepage, registration page queued, contact page queued) so that when the site does eventually go down, the artifact is preserved publicly.
- IC3: a US IC3 complaint goes in with the case file attached.
If any of those complaints lands a takedown, I will update the case file with the date and the responding party, and the status badge above will flip from "still live" to "taken down".
takeaways
If you only remember a few things from this:
- A stranger who follows you first and opens with "Hello" three days before mentioning money is running a script. The slow tempo is the script.
- "Profits of $X in 2025" with no auditable source is a number designed to anchor your sense of what is normal. It is not normal.
- A "trading platform" with a Skip button on KYC is not a trading platform.
- Generic landing copy plus a TradingView widget plus a Smartsupp chat bubble plus a registration form asking for full address and DOB is a fingerprint, not a coincidence. You will see this exact configuration on a different domain next month.
- Once they have your ID, the cash loss is no longer the worst part of the story.
This one is still live as of 2026-04-29. I will check back.